
A SYN flood is a form of denial-of-service attack on data communications in which an attacker rapidly initiates a connection to a server without finalizing the connection. The server has to spend resources waiting for half-opened connections, which can consume enough resources to make the system unresponsive to legitimate traffic.[1][2]
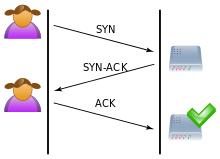
The packet that the attacker sends is the SYN packet, a part of TCP's three-way handshake used to establish a connection.[3]
- ^ "CERT Advisory CA-1996-21 TCP SYN Flooding and IP Spoofing Attacks" (PDF). Carnegie Mellon University Software Engineering Institute. Archived from the original on 2000-12-14. Retrieved 18 September 2019.
- ^ New York's Panix Service Is Crippled by Hacker Attack, New York Times, September 14, 1996
- ^ "What is a DDoS Attack?". Cloudflare.com. Cloudflare. Retrieved 4 May 2020.